January 24, 2017
Back at the end of last year, Doctor Web security researchers noted the growing number of malicious programs for Linux. And at the end of January, they detected several thousand Linux devices infected with a new Trojan.
The Trojan, used by cybercriminals to infect numerous Linux network devices, has been named Linux.Proxy.10. As the name of this malicious program suggests, it is designed to run a SOCKS5 proxy server on the infected device on the basis of the freeware source code of the Satanic Socks Server. Cybercriminals use this Trojan to ensure that they remain anonymous online.
To distribute Linux.Proxy.10, cybercriminals log in to the vulnerable devices via the SSH protocol, and at the same time the list of devices, as well as the logins and passwords that go with them, are stored on their server. The list looks like this: «IP address:login:password». It is notable that users with such account details are usually created by other Linux Trojans. In other words, Linux.Proxy.10 infiltrates computers and devices that either have standard settings or are already infected with Linux malware.
A script is generated with the help of this list, and it runs on the infected devices using sshpass. It infects the attacked system with Linux.Proxy.10.
Besides that, the server belonging to the cybercriminals who distribute Linux.Proxy.10 has been found to contain not only the lists of vulnerable devices. Doctor Web security researchers also detected a Spy-Agent administrator panel and a build of Windows malware from a known family of Trojan spyware, BackDoor.TeamViewer.
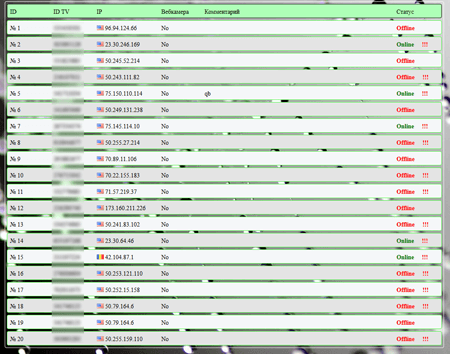
To connect to a proxy server that is launched using Linux.Proxy.10, cybercriminals have only to know the IP address of the infected device and the port number saved in the body of the Trojan during its compilation. Doctor Web security researchers have succeeded in counting the number of devices infected with Linux.Proxy.10: as of January 24, 2017, it runs into the several thousands.
To protect devices from Linux.Proxy.10 when infection is suspected, it is recommended that they be scanned remotely via the SSH protocol using Dr.Web Anti-virus 11.0 for Linux.
Source: http://news.drweb.com/show/?i=11115&lng=en&c=14





