August 15, 2016
Doctor Web already published a news article about the Trojan that takes advantage of TeamViewer’s remote control utility. This time, the company’s specialists have detected yet another backdoor that installs legitimate TeamViewer components on infected machines for the purpose of spying on users.
The Trojan, named BackDoor.TeamViewerENT.1, is distributed under the name Spy-Agent, a name it shares with its system management interface. Cybercriminals have been developing this malware program since 2011 and regularly release modified versions of it. This article will focus on one such modification.
Like its counterpart BackDoor.TeamViewer.49, BackDoor.TeamViewerENT.1 is a multi-component Trojan. However, while its predecessor implemented TeamViewer only to upload a malicious library to an attacked computer’s memory, BackDoor.TeamViewerENT.1 uses this utility to spy on potential victims.
The Trojan’s main payload is placed into the avicap32.dll library, and its operation parameters are stored in an encrypted configuration block. BackDoor.TeamViewerENT.1 also saves the files and folders necessary for TeamViewer to operate, together with some additional files.
If a Windows program needs a dynamic library to be loaded in order to operate, the system starts searching for the file with that name in the same folder from which the program was run, and only then in the Windows system directory. Virus makers decided to take advantage of this Windows feature: TeamViewer needs a standard avicap32.dll library, which is stored in one of the default system catalogs. However, the Trojan stores a malicious library with that same name right in the folder with the original TeamViewer executable file, and, as a result, Windows loads the malicious library, rather than the legitimate one, into the memory.
Once launched, BackDoor.TeamViewerENT.1 disables error messaging for the TeamViewer process, appends its files and the TeamViewer files with the attributes “system”, “hidden”, and “read only”, and then intercepts calls for TeamViewer functions and calls for several system functions. If certain files or components are missing in order for TeamViewer to operate normally, the Trojan downloads them from its command and control (C&C) server. In addition, if BackDoor.TeamViewerENT.1 detects that the Windows Task Manager or Process Explorer has been launched, the Trojan terminates the TeamViewer process. When connected to the C&C server, the backdoor can perform the following functions:
- Restart the computer
- Turn off the computer
- Remove TeamViewer
- Relaunch TeamViewer
- Start listening through the microphone
- Stop listening through the microphone
- Identify the web camera
- Start viewing via the web camera
- Stop viewing via the web camera
- Download a file; then save it to a temporary folder and run it
- Update a configuration file and the backdoor’s executable file
- Connect to the specified remote server; and then run cmd.exe and execute input/output redirection to a remote server
Once executed, these commands provide cybercriminals with great opportunities to spy on users and steal their personal information. In particular, we know that virus makers have used this Trojan to install malware programs belonging to the Trojan.Keylogger and Trojan.PWS.Stealer families. In the course of their investigation, Doctor Web’s security researchers found out that the backdoor targets residents of particular countries and regions at different times. For example, in July, BackDoor.TeamViewerENT.1 attacked user computers in Europe, particularly in Great Britain and Spain, and, in August, cybercriminals shifted their focus to the USA.
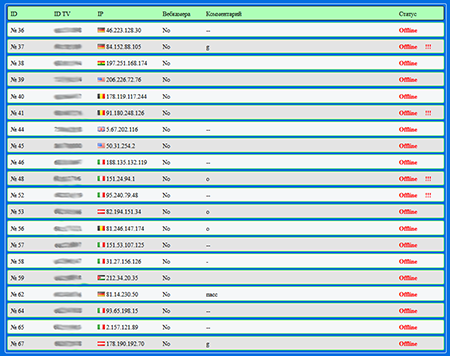
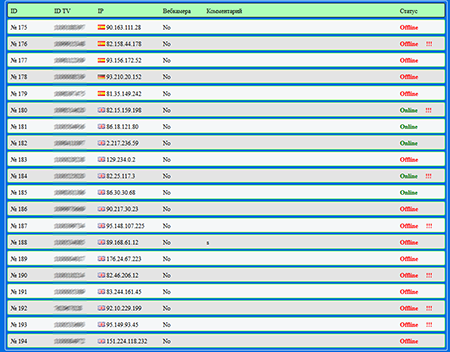
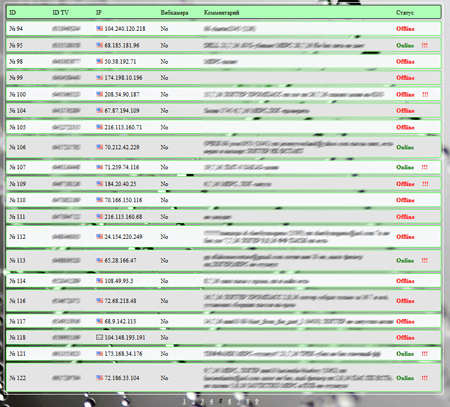
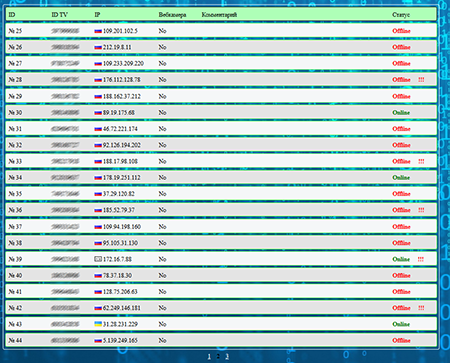
Nevertheless, a large number of cases involving this Trojan were also registered in Russia:
Doctor Web specialists are keeping a close watch on this Trojan and recommend that users be more careful and update their virus databases in a timely manner. Dr.Web Anti-virus successfully detects and removes BackDoor.TeamViewerENT.1, so it does not pose any threat to Dr.Web users.
View the article